Solutions
From collaboration to innovation, let us partner with your business to meet your needs. Use all our local and global expertise, along with our cloud, networking and security services to drive your business to the next level.

Sustainability
Digital solutions hold the key to helping you achieve your sustainability goals. We’re committed to helping you use digitalisation to smooth and speed your journey to net zero.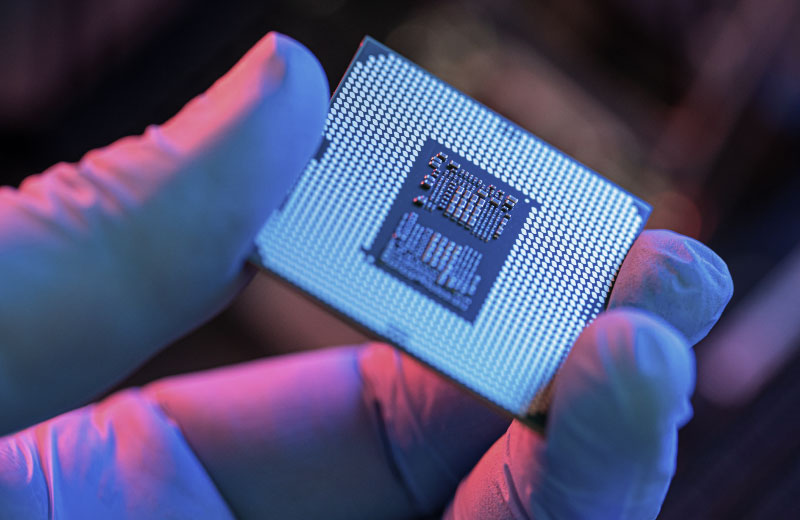
Explore by industry
With over seventy years of delivering services to companies in every sector, in every corner of the world, we know the best approach is less talk and more action.Explore our products and services
Discover how our products and services can simplify your infrastructure, build agility into your business, balance the risk and reward of the cloud, and make security integral to your business.
Operator Connect for Microsoft Teams
Integrate calling and audio conferencing into Microsoft Teams
Key benefits
Deploy Operator Connect quickly into your Microsoft Teams
Reduce the cost of maintaining a physical phone system with a cloud-based solution
Bundled digital user adoption support to bring faster business results
Virtual Events
Take your online events to the next level with our managed service
Key benefits
Choose either Microsoft Teams, Zoom or Webex to run your event
Let us take care of the planning, organising, and running of your event
Deliver an improved audience experience, with interactive engagement features
Webex Calling
Turn your Webex into a cloud-based phone system, with the power of our global voice network
Key benefits
Operate with top-grade security assured by both Cisco and BT Security experts
Keep your organisation connected with built-in, site level resilience
Get expert design, deployment and user adoption services and reduce the risks associated with voice transformation
Why BT?
With one of the largest security capabilities in our industry, we deliver exceptional products and services to customers in 180 countries across the globe.
95%
of FTSE 100 trust us
95% of FTSE 100 companies are working with us to help deliver their connectivity needs.
£2.8bn
Five year R&D investment
We’ve invested £2.8bn in research and design over the last five years, ensuring that our offer meets our customer’s needs.
2023
Gartner® recognised leader
In 2023 we were recognised by Gartner® as a Magic Quadrant™ Leader for Network Services.
6.5k
Daily cyber attacks stopped
We defend ourselves and our customers from over 6,500 cyber attacks each day
Would you like to talk to an expert?
From products to solutions, discover how we can transform your business connectivity.